For a few hours in March, Syria’s official presence on X descended into chaos. Verified government accounts began posting pro-Israel messages, retweeting explicit content, and even briefly renaming themselves after Israeli political figures. The posts included phrases like “Glory to Israel,” which quickly spread across the platform before authorities regained control.
At first glance, it looked like political trolling or a coordinated propaganda stunt. But reporting a new report suggests the real story was far more revealing: a government still struggling with the basics of digital security.
According to a WIRED magazine report, several official Syrian government accounts were compromised, including those linked to the presidency’s General Secretariat, the Central Bank, and multiple ministries.
The Ministry of Communications and Information Technology said it took “urgent steps” to restore the accounts and prevent further breaches. Within days, most of the profiles had returned to normal.
Cybersecurity researchers who spoke to WIRED said that the Syrian incident pointed to familiar vulnerabilities rather than a sophisticated geopolitical operation.
“We still do not know exactly what happened,” said Noura Aljizawi, a senior researcher at Citizen Lab, to WIRED. “Whether the accounts were directly hacked or accessed through weak or reused credentials, the conclusion is much the same: very poor digital security practices.”
A pattern stood out to cybersecurity analysts. “The fact that several official accounts seemed to fall in quick succession suggested some form of centralized control,” Muhannad Abo Hajia, a cybersecurity expert at Damascus-based group Sanad, told the magazine. “That kind of setup is not inherently wrong, but only if proper safeguards are in place.”
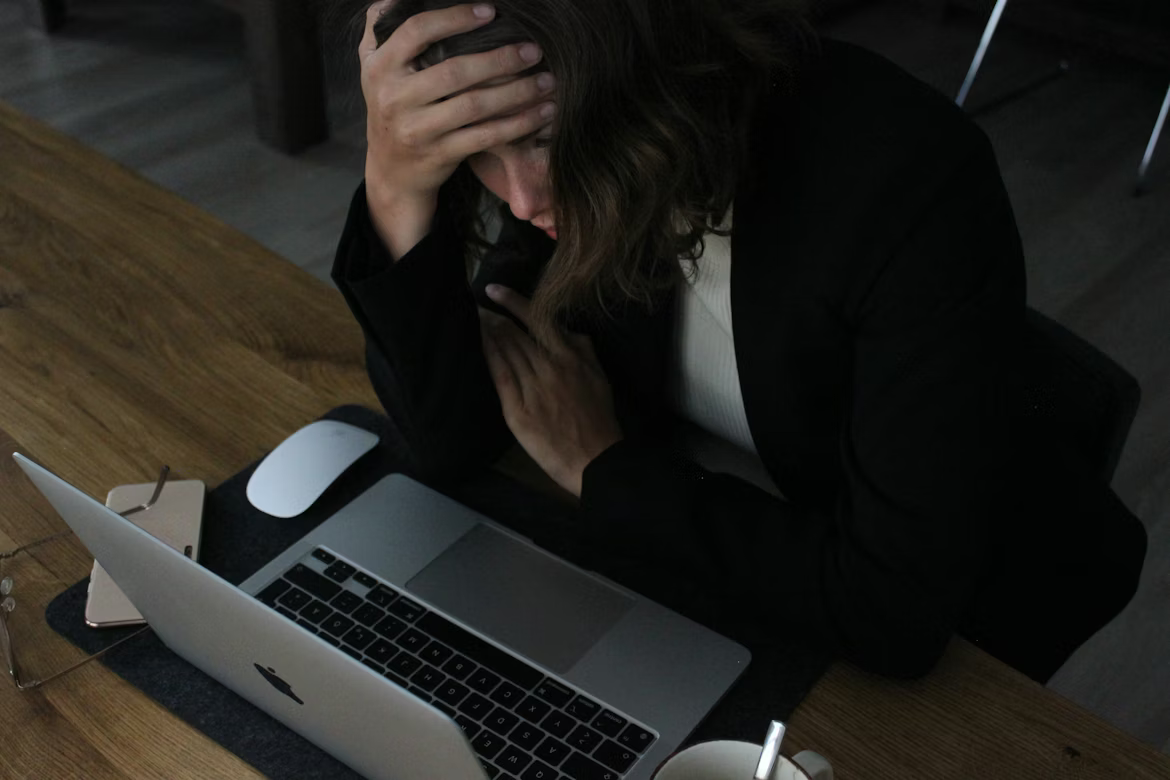
Password reuse, phishing emails, compromised recovery accounts, and missing multi-factor authentication remain common entry points for attackers.
“Account takeovers like this usually result from familiar vulnerabilities,” a cybersecurity engineer, Rinad Bouhadir, told WIRED. “Phishing, weak credentials, compromised recovery emails, or the absence of MFA.” Those weaknesses can create a domino effect. If multiple government accounts rely on the same login details or recovery channels, a single compromise can spread across institutions in minutes.
“The current authorities inherited a near-nonexistent cybersecurity system,” said Syrian cybersecurity specialist Dlshad Othman. “Repairing it has yet to become a real priority.” Mohammad Mostafa, a digital expert at Sync, believes the breach likely came down to basic mistakes.
“This could have been a phishing attempt against a communications staffer, password reuse across several accounts, or a compromised recovery email tied to multiple profiles,” he said. “None of those scenarios requires elite capability. They require basic lapses.”