Microsoft has disclosed a new cyberattack dubbed the ClickFix campaign. The scheme uses social engineering to trick victims into opening Windows Terminal and pasting a malicious command, which sets off a chain of actions that ultimately installs the data-stealing malware known as Lumma Stealer.
The technique surfaced in February 2026 and represents a subtle shift in how ClickFix attacks operate. Earlier versions typically directed victims to open the Windows “Run” dialogue and paste in a command. Security tools and analysts began flagging that behaviour. Attackers appear to have noticed.
Now the instructions guide users to open Windows Terminal using a shortcut: Windows + X, then I.
According to Microsoft’s threat intelligence team, the change matters because the terminal environment looks more legitimate to users.
“This campaign instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly,” the researchers explained. “Guiding users into a privileged command execution environment that blends into legitimate administrative workflows and appears more trustworthy.”
The trick typically begins on a fake verification page, sometimes disguised as a CAPTCHA prompt or troubleshooting message. The page provides a command for the user to copy and paste into the terminal.
On the surface, it looks like part of a verification step.
But behind the scenes, the command is heavily obfuscated. Once pasted, it launches additional PowerShell and terminal processes that decode the script and begin pulling down more components.
From there, the attack escalates quickly.
The script downloads a compressed payload along with a renamed version of the popular archiving utility 7-Zip. That tool quietly extracts additional malware files, setting off a multi-stage operation that retrieves more payloads, modifies security settings, and establishes persistence through scheduled tasks.
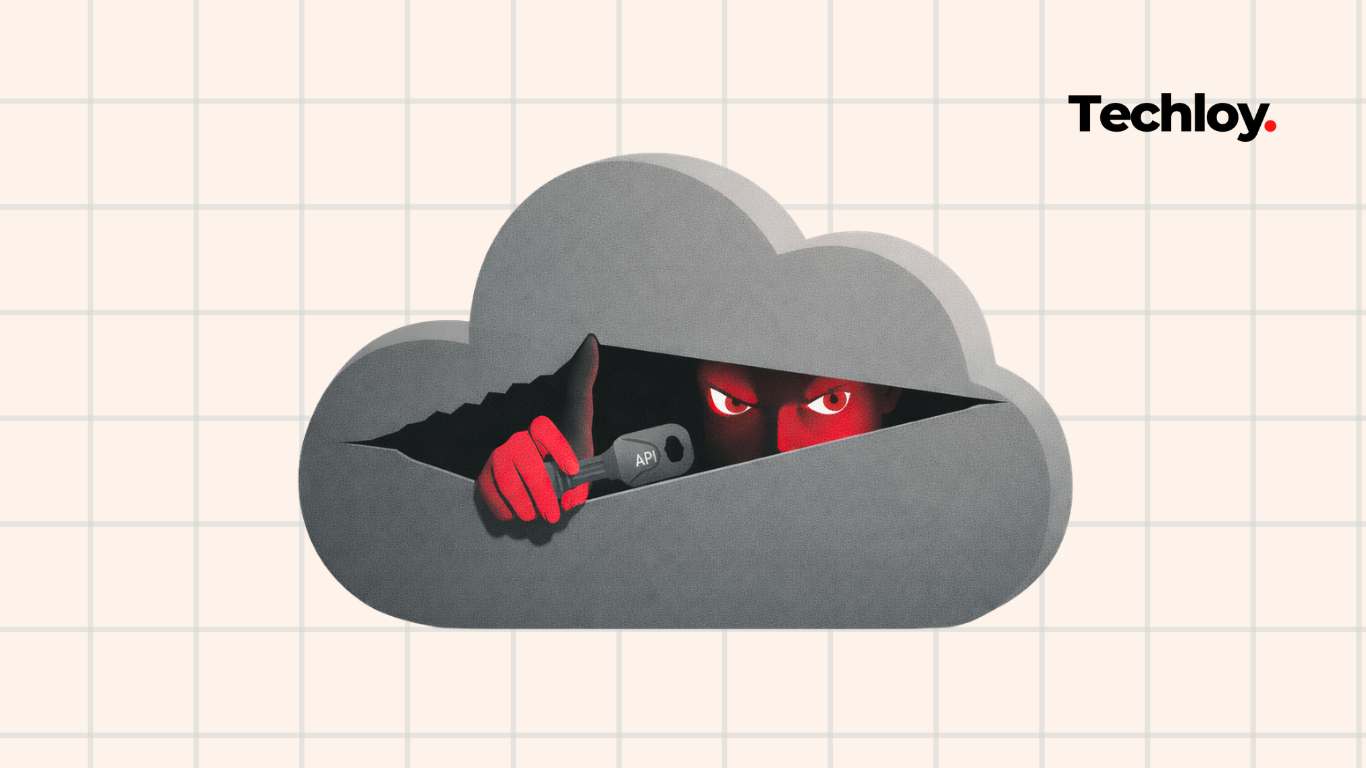
“The stealer targets high-value browser artifacts, including Web Data and Login Data, harvesting stored credentials and exfiltrating them to attacker-controlled infrastructure,” Microsoft said.
The malware injects itself into running browser processes such as Chrome and Edge using a technique called QueueUserAPC, allowing it to capture sensitive information without immediately triggering suspicion.
Researchers also observed an alternate attack path. In that scenario, the command downloads a batch script that writes a Visual Basic script to a temporary folder before abusing legitimate system tools like MSBuild to continue execution. The script even connects to blockchain infrastructure, a tactic sometimes used to hide malicious communications within normal network traffic.
How to protect yourself
The first line of defence is simple caution. If a website or pop-up message instructs you to open Windows Terminal, PowerShell, or the Run command and paste a piece of code, treat it as a major red flag. Legitimate websites and software updates rarely ask ordinary users to manually run commands.
Keeping your operating system and security software up to date also reduces the risk of infection. Regular updates to Microsoft Windows and your antivirus tools help detect suspicious scripts and block known malware families such as Lumma Stealer.
Another practical step is to rely on official sources for software downloads and troubleshooting instructions. If you encounter a prompt claiming that your browser or system needs fixing, close the page and verify the information through trusted vendor sites instead of following on-screen instructions.